Link to the room: https://tryhackme.com/room/socworkbookslookups.
[Task 2] Assets & Identities
Looking at the identity inventory, what is the role of R.Lund at the company?
Check the “Role” column in the identity inventory table for R.Lund.
Checking the asset inventory, what data does the HQ-FINFS-02 server store?
Check the “Purpose” column in the asset inventory table for HQ-FINFS-02.
Finally, does the file sharing from the scenario look legitimate and expected? (Yea/Nay)
[Task 3] Network Diagrams
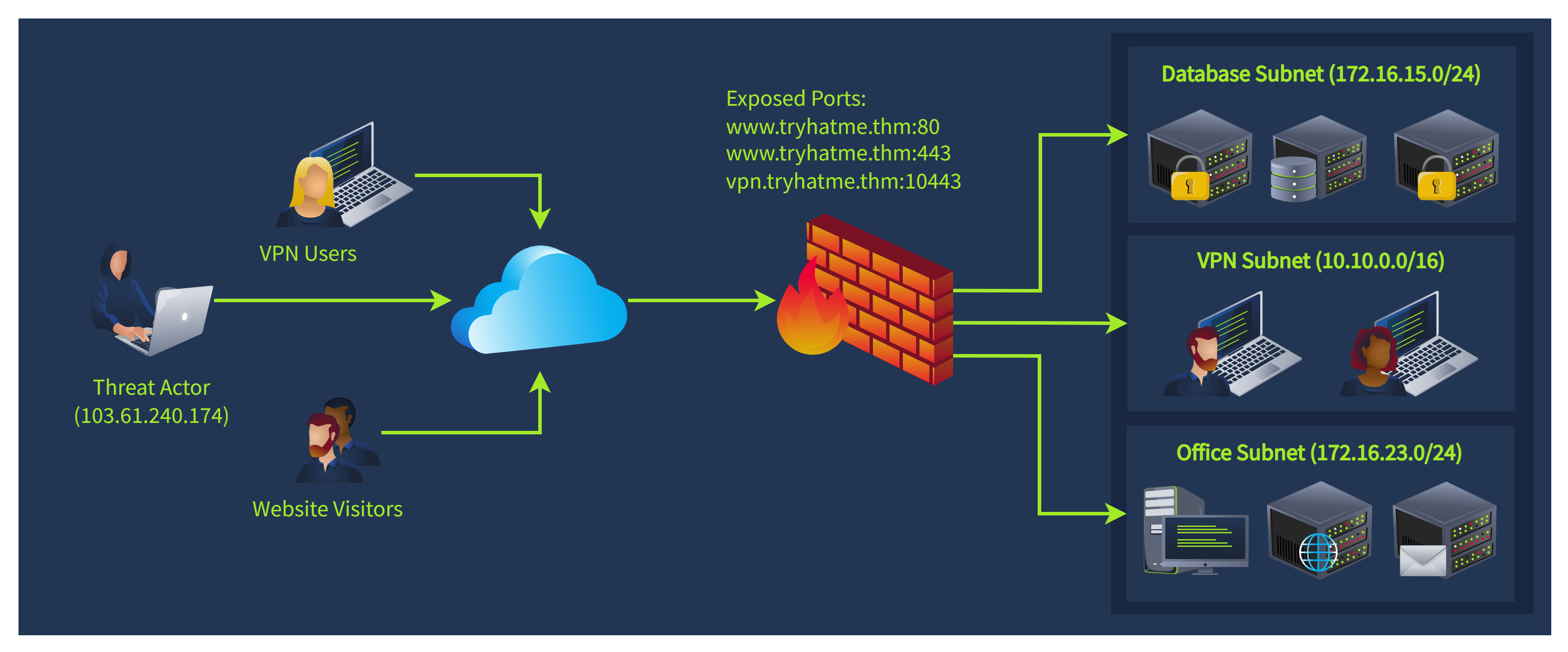
network diagram
According to the network diagram, which service is exposed on the TCP/10443 port?
Now, which subnet would the server behind 172.16.15.99 IP belong to?
Finally, does the scenario look like a True Positive (TP) or False Positive (FP)?
VPN brute force, DB scan, switching subnets is something that can turn on your inner SOC radar.
[Task 4] Workbooks Theory
Unusual Login Location Workbook
Which SOC role would use workbooks the most (e.g. SOC Manager)?
What is the process of gathering user, host, or IP context using TI and lookups?
Enrichment: Use Threat Intelligence and identity inventory to get information about the affected user
Review the enrichment stage in the workbook.
[Task 5] Workbooks Practice
What flag did you receive after completing the first workbook?
1
| THM{the_most_common_soc_workbook}
|
What flag did you receive after completing the second workbook?
1
| THM{be_vigilant_with_powershell}
|
What flag did you receive after completing the third workbook?
1
| THM{asset_inventory_is_essential}
|