Link to the room: https://tryhackme.com/room/introtopipelineautomation.
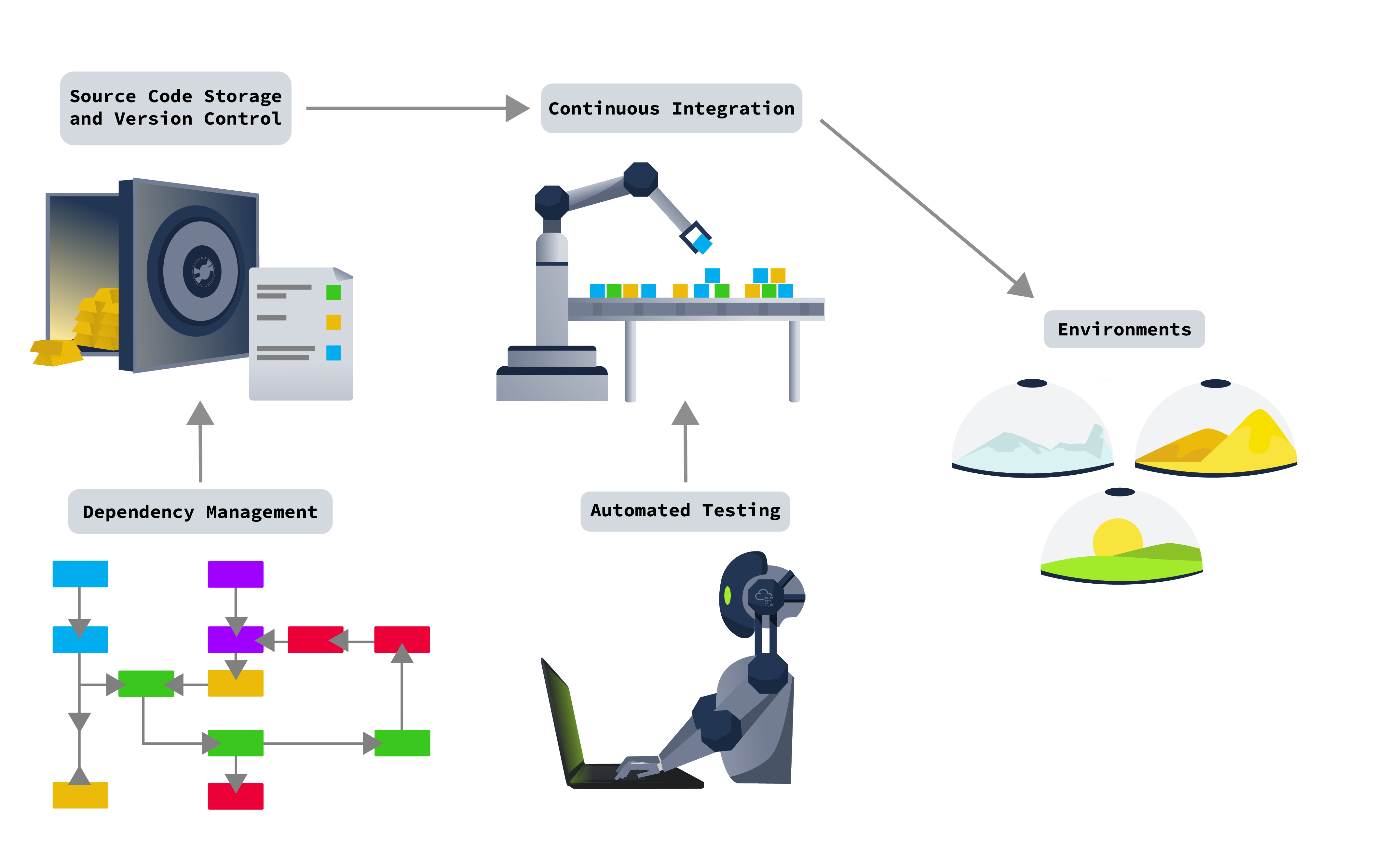
[Task 2] DevOps Pipelines Explained
Where in the pipeline is our end product deployed?
[Task 3] Source Code and Version Control
Who is the largest online provider of Git?
GitHub is by far the largest provider of Internet hosting for software development and version control using Git.
What popular Git product is used to host your own Git server?
You could also host your own git server using software such as Gitlab.
If an attacker got access to the repo, they could use a tool such as GittyLeaks, which would scan through the commits for sensitive information.
[Task 4] Dependency Management
What do we call the type of dependency that was created by our organisation? (Internal/External)
What type of dependency is JQuery? (Internal/External)
What is the name of Python’s public dependency repo?
Example external dependency managers:
PyPi for Python,- NuGet for .NET,
- and Gems for Ruby libraries.
What dependency 0day vulnerability set the world ablaze in 2021?
A 0day vulnerability was discovered in Log4j dependency in 2021 called Log4Shell. Log4j is a Java-based logging utility. It is part of the Apache Logging Services, a project of the Apache Software Foundation. The vulnerability could allow an unauthenticated attacker to gain remote code execution on a system that makes use of the logger. The true issue? This small little dependency was used almost literally everywhere.
[Task 5] Automated Testing
Static Application Security Testing (SAST) works by reviewing the source code of the application or service to identify sources of vulnerabilities.
One method that DAST tools use to find additional vulnerabilities, such as Cross Site Scripting (XSS), is by creating sources and sinks.
Can SAST and DAST be used as a replacement for penetration tests? (Yea,Nay)
Sadly, SAST and DAST tools cannot fully replace manual testing, such as penetration tests. There have been significant advancements in automated testing and even in some cases, these techniques were combined with more modern approaches to create new testing techniques such as Interactive Application Security Testing (IAST) and Runtime Application Self-Protection (RASP).
[Task 6] Continuous Integration and Delivery
What does CI in CI/CD stand for?
What does CD in CI/CD stand for?
What do we call the build infrastructure element that controls all builds?
A build orchestrator directs the various agents to perform the actions of the CI/CD pipelines as required.
A build agent is a software component, typically a program or a virtual machine, that executes the tasks and steps defined in a build pipeline.
[Task 7] Environments
Which environment usually has the weakest security configuration?
The DEV environment is the playground for developers. This environment is the most unstable as developers are continuously pushing new code and testing it. From a security standpoint, this environment has the weakest security.
Which environment is used to test the application?
The UAT environment is used to test the application or select features before they are pushed to production.
Which environment is similar to PROD but is used to verify that everything is working before it is pushed to PROD?
The PreProd environment is used to mimic production without actual customer/user data.
What is a common class of vulnerabilities that is discovered in PROD due to insecure code creeping in from DEV?
Developer bypasses allow developers to quickly test different application features by bypassing time-consuming features such as MFA prompts. A common example is having a specific One-Time Pin (OTP) code that is always accepted, regardless of the OTP code that is sent by the application.
[Task 8] Challenge
What is the flag received after successfully building your pipeline?
1
| THM{Pipeline.Automation.Is.Fun}
|